Retail has emerged as the third most attacked industry in Canada, accounting for 10 per cent of all attacks that IBM X-Force remediated in 2022. It came behind energy and utilities, which constituted 60 per cent of attacks in Canada, followed by finance and insurance at 20 per cent.
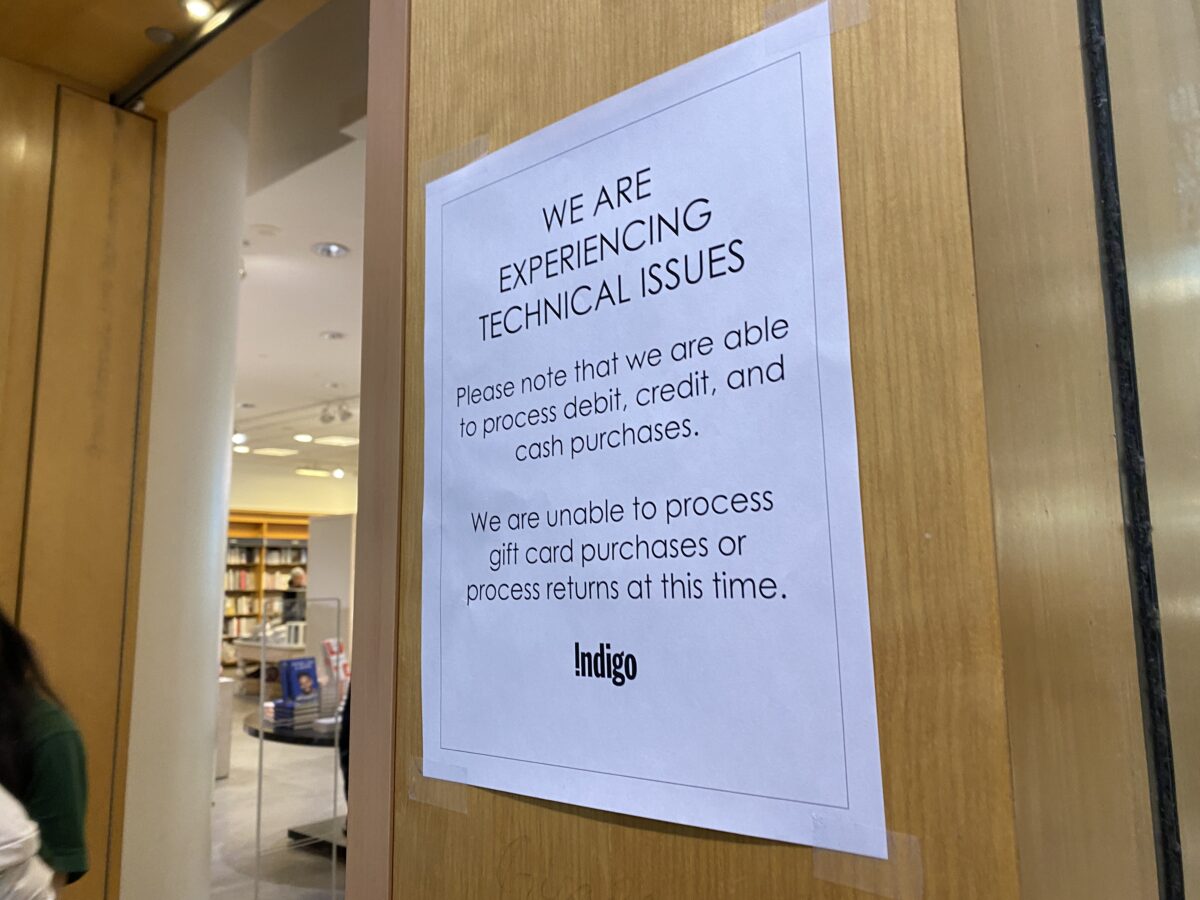
As a growing list of Canadian retailers fall victim, IBM says the focus should be on rolling out the right technology to prevent these attacks from happening in the first place.
An IBM X-Force study said extortion was used in more than a quarter of attacks – criminals are swarming vulnerable industrial systems to disrupt critical operations that can’t afford to be down (like utilities, manufacturing, and banking) and making them pay.
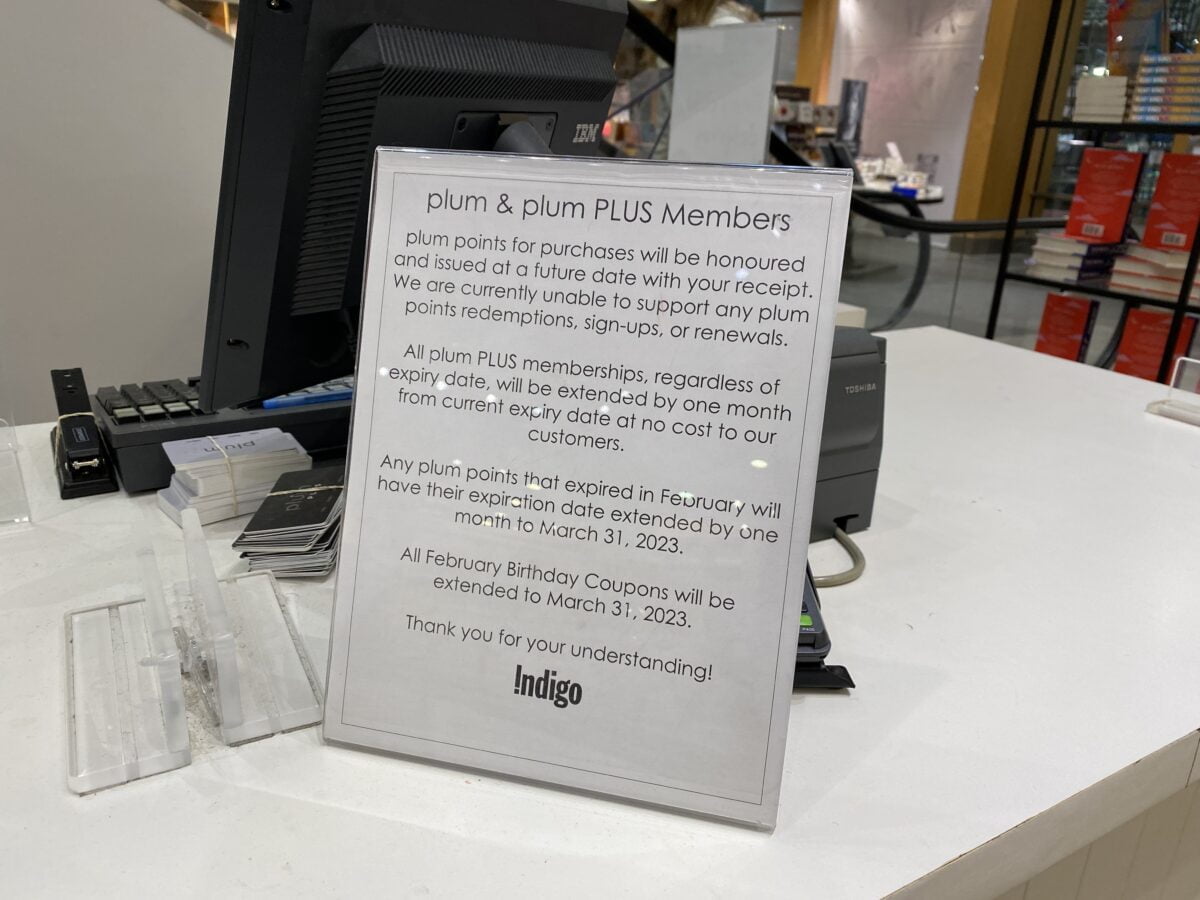
The report said data breaches are costing Canadian companies CA$7.05 million per incident on average (an all-time high) – the financial stakes and threat to brand reputation are more significant than ever.
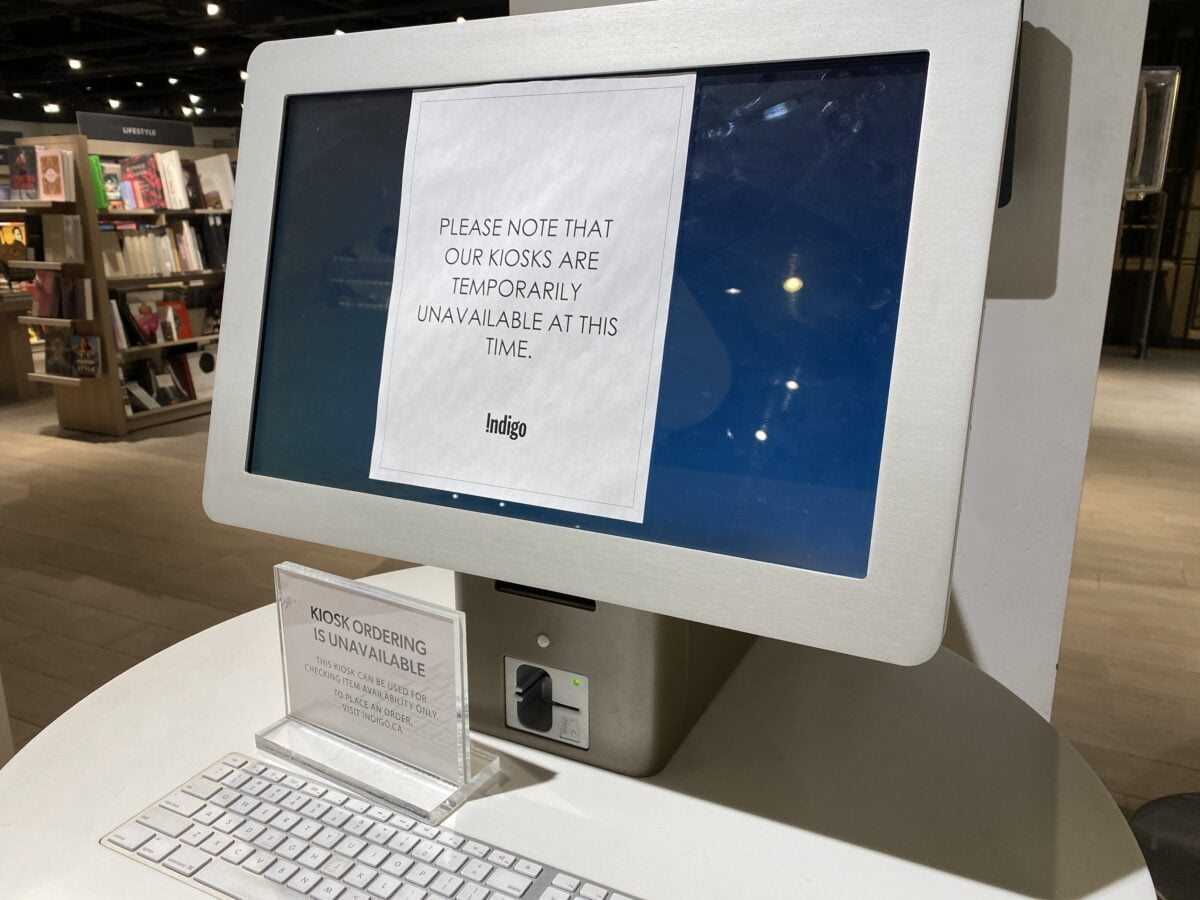
Evan O’Regan, Associate Partner in Security Services for IBM, said the findings of the report shed light on the growing threat to the retail and wholesale sector, which is an attractive target for cyber attackers due to its large amounts of sensitive information and financial transactions, its reliance on a complex supply chain network, and the potential for significant reputational damage.

“This is real data based on our X-Force team responding to actual incidents both globally and in Canada,” said O’Regan.
“The threat to the retail industry is very real. A good example of that is if you look at Canada and North America, it’s in the top three targeted, exploited regions and retail which includes wholesale is in the top three of the exploited industries in Canada.
“I think it’s inherent to the nature of the industry. The first thing that I would call out is we need to look beyond the cash register. While it is true, we’ve seen a massive increase of online shopping, that is a trend and it continues to increase but it’s not just about breaking in and stealing credit card information. In fact, the targeting of your credit cards is going down for a couple of reasons. One, they’re better defended both by the banks and the retail industry but also on the black market, on the dark web, you’re only getting about 10 bucks per validated credit card record.
“But when you’re doing these transactions online you need to collect a fair amount of information about the person that you’re doing business with and that is extremely valuable on the dark web. Your exploiters can sell that and as well an organization is compromised. So if I’m a hacker and I’ve been able to land and create backdoor access to your organization I can sell that for $10,000 on the dark web for somebody else to use the work that I’ve done to launch a more sophisticated exploit.
“Why it’s important . . . is first of all you’re doing business with a lot of people. Second, is a reliance on a complex supply chain . . . When you look at the types of threats, extortion is one of the number attacks, and high psychological impact attacks. Some of the major brands can probably recover from a bad headline but if I’m shopping between a retailer that I know or heard has been compromised versus one that hasn’t been in the news, that can have a massive impact on the bottom line.”
O’Regan said the retail sector on the whole has this exposure.
“It’s a lucrative target for the attackers. You have to remember they’re running a business. When we link it to the notion about the threat being real, look at some of the other industries,” said O’Regan. “These are people that would shut down a hospital. These are people that would shut down a utility. Nothing that is out of bounds. We passed that rubicon a long time ago.
“So if they see an opportunity, they’re going to take it.”
IBM Security X-Force said in Canada, credential harvesting took the pole position with 67 per cent of incidents that X-Force remediated (compared to 11 per cent globally). A third of them (33 per cent) resulted in botnet (malware) infections of networks. Overall, X-Force saw threat actors use spearphishing links and exploitation of public-facing applications in equal proportion to gain initial access. Botnets, ransomware, and deployment of recon/scanning tools were the three top actions on objectives observed in incidents in Canada.

Here are IBM Security’s recommendations:
- Stop blaming the user. Attackers rely on the fact people are innately curious and inclined to click on links. The report shows that it’s a strategy that works – with 41 per cent of incidents starting from a phishing email. The default industry setting is to blame the user – that needs to change. The focus should be on rolling out the right technology to protect users from falling victim.
- Accelerate your response. It’s no longer a question of whether an adversary will get in – it’s a question of when. Successfully responding to a breach is all about speed and limiting the window of access and damage to your environment. How your team responds in the critical moment can make all the difference in the amount of time and money lost in a response.
- Employ endpoint or extended detection and response technologies. The rise in backdoor cases points to some success in catching infections earlier. Endpoint and extended detection and response technologies provide the means to identify and mitigate threats before adversaries take more dangerous actions.
- Shift your mindset. You have to think like an attacker and understand how they operate. Adversary simulations and threat hunting can help businesses outsmart cybercriminals.
- Know your attack surface. One third of attackable assets on organizations networks are unmanaged or unknown, offering easy targets for attackers and risking unintended data exposure. You need to think like an attacker, discover where you’re exposed and the ways an attacker could get in with least detection.
- Challenge assumptions. Today, you have to assume compromise. Perform regular offensive testing including threat hunting, penetration testing, and objective-based red teaming to detect or validate opportunistic attack paths into your environment.
- Build an adaptable, threat-driven security strategy. There is no single, out-of-the-box solution to protecting businesses today. Attackers are constantly innovating and evolving techniques to evade detection – cyber strategies should be just as flexible. Buy the tools, build the plan, but then test it, learn from what you find, and adapt regularly to consider the rapidly evolving threat landscape.
O’Regan said it’s important for companies to get their house in order and start looking for some of these known exploits inside of their organization, inside of their operations.
“The retail industry needs to have something of a security strategy and a threat driven plan that reflects the threat that they are facing because there’s no single out of box solution. The attacker is going to constantly innovate so it’s something that becomes a living, breathing document that gets revisited. It’s a practice. It’s the notion of building the plan, making sure you have the right tools to support it, learn from what you find and adapt regularly because it’s a rapidly evolving threat landscape so you’re response to that has got to be rapidly evolving,” he said.














